The Caesar Cipher: Rome's Gift to Cryptography
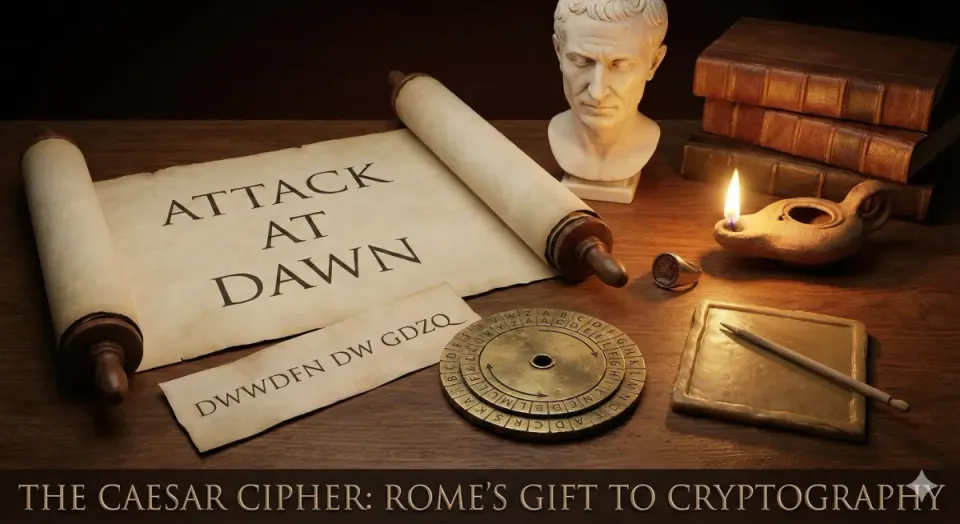
Among the earliest documented encryption techniques in recorded history, the Caesar Cipher holds a deceptively simple yet foundational place in the science of cryptography. Named after Julius Caesar, who reportedly used it to protect sensitive military correspondence around 58–50 BCE, it represents one of the first systematic applications of what cryptographers call a substitution cipher.
How It Works
The mechanism is elegant in its simplicity: every letter in a plaintext message is shifted a fixed number of positions along the alphabet. With a shift of 3 — Caesar's preferred key — A becomes D, B becomes E, and Z wraps around to C. The shift value is the secret key, shared only between sender and recipient.
Formally, the encryption function is expressed as C = (P + k) mod 26, where P is the plaintext letter's position (0–25), k is the shift key, and C is the resulting ciphertext position.
Cryptographic Weaknesses
From a modern perspective, the Caesar Cipher is trivially broken. Its keyspace contains only 25 meaningful possibilities — a brute-force attack requires at most 25 attempts. Furthermore, because it is a monoalphabetic substitution cipher, it preserves the natural frequency distribution of letters. An attacker using frequency analysis — a technique formalized by the Arab polymath Al-Kindi in the 9th century — can identify the shift by simply matching the most common ciphertext letter to the most frequent letter in the target language (E in English).
Enduring Legacy
Despite its cryptographic fragility, the Caesar Cipher introduced the core vocabulary of the entire field: keys, plaintext, and ciphertext. It is the direct ancestor of more complex systems like the Vigenère cipher and, conceptually, the one-time pad. Today it remains an indispensable pedagogical tool, providing a clear and intuitive entry point into modular arithmetic, cryptanalysis, and the principles that underpin modern algorithms like RSA and AES.
Sometimes, the simplest ideas cast the longest shadows.
